If you are a parent, you may have seen your child devastated after losing their in-game possessions to a griefer. Or if you are a Minecraft gamer yourself, you may have been directly affected. Griefers are gamers, who deliberately destroy other players’ builds, steal in-game items or disrupt other players. After such an experience, it is natural to wish for a safer, grief-free environment.
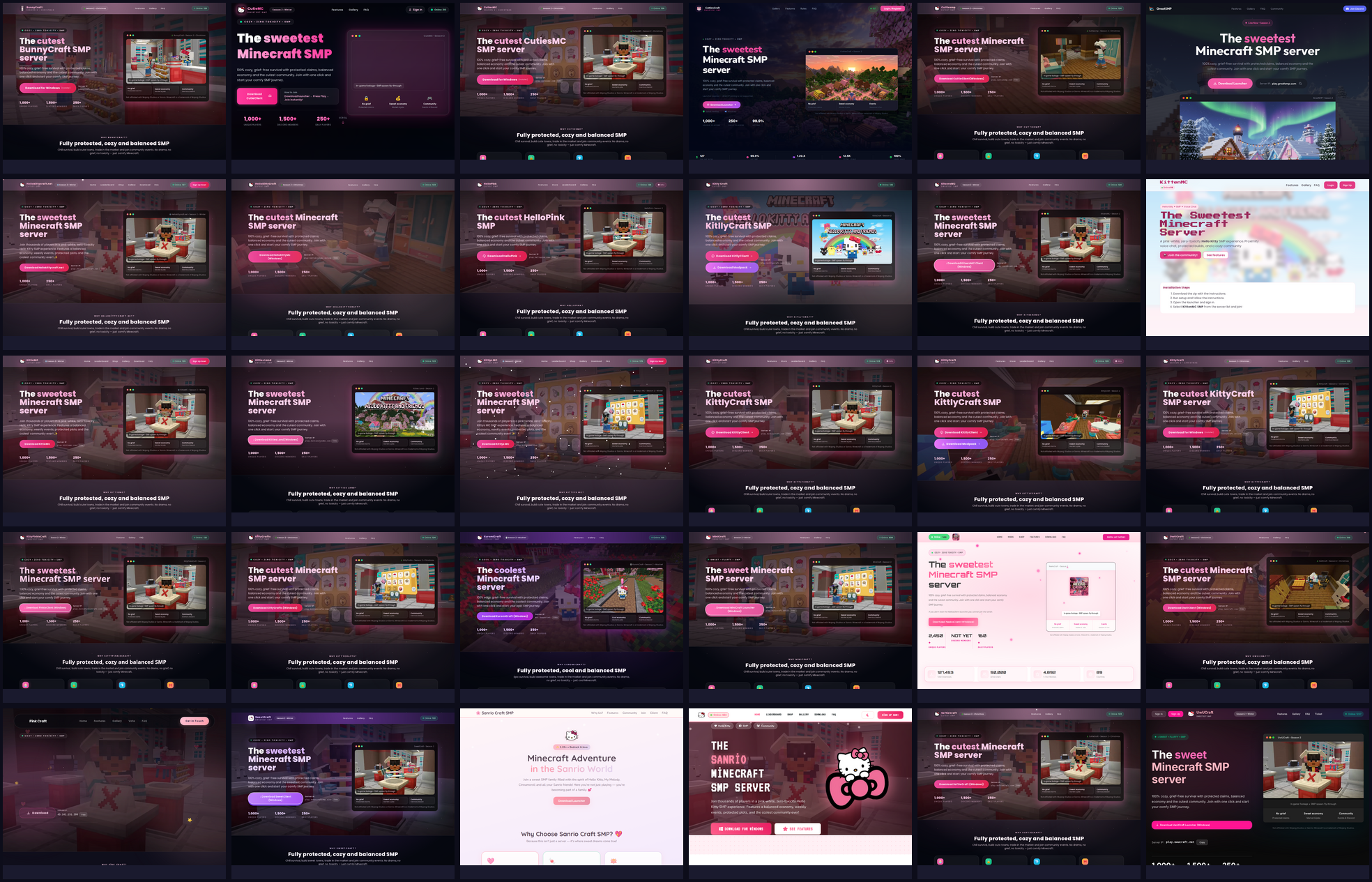
There are Minecraft communities that promise just that: “cozy grief-free survival with protected claims” or “no drama, no grief, no toxicity”, as seen on Minecraft websites such as sugarsmp(dot)com (see figure 1).
Indeed, if we check the download links of SugarSMP, they lead to cobblemon-themed mod packs, there are roughly 35-45 players online with small fluctuations, the site is full of videos and photos of the community’s creations, there are FAQs, a page with testimonies and a section showcasing the staff. So far everything looks fine, does it?
There are even videos on Youtube from other players showcasing live streams of their SugarSMP server experience. Server listings that promote the server as a good choice if you want to play Minecraft online.
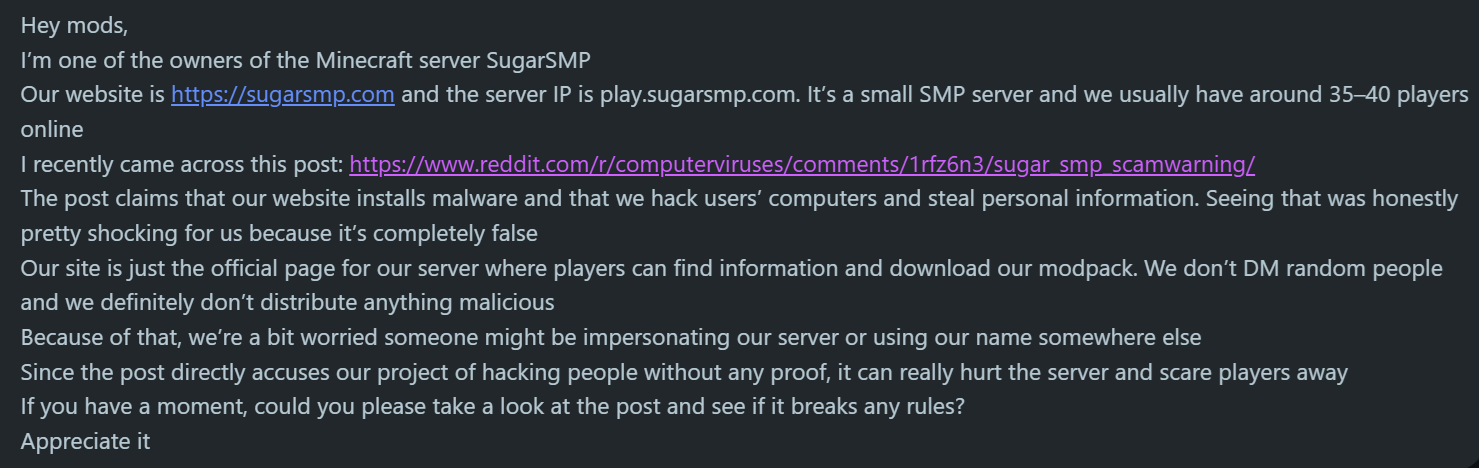
Given this information, imagine that the owner of SugarSMP politely requested you to take down a post that claims they are spreading malware. Would you agree to do so?
This happened to moderators of r/computerviruses. They received the following message from a reputable user account that has been active on Reddit for almost a decade.
Following this, we - that is rifteyy who is a moderator on r/computerviruses, a second collaborator (who chose to remain nameless) and myself - decided to dig deeper. Although the SugarSMP website looks fine on the surface, a few things just felt "off".
For instance, while there are constantly 35-45 players shown online, there was never any substantial fluctuation. Assuming the players only log in from one time zone, we would have expected to see sharp drops corresponding to times when most players are typically sleeping, or spikes when they are awake and enjoy their free time with a Minecraft game. But even assuming that players from different time zones are using the server, there should be a higher fluctuation.
Investigation
The FAQ section of the SugarSMP website says “SugarSMP runs on Fabric 1.21.4 and is fully modded”, which means you can only join the server if you install the required mod package. Indeed, when trying to connect to the server, it requests the mod package from sugarsmp(dot)com/downloads.
This is on its own not suspicious, because Fabric requires that the mods on your client match those of other players. But could this be abused to coerce users into downloading malware?
Minecraft servers use the Server List Ping (SLP) protocol to talk to clients. So we wrote a small script to ping it and get back basic information from the game server.
import socket, struct, json, sys
sock = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
sock.settimeout(10)
host = sys.argv[1]
sock.connect((host, 25565))
host_bytes = host.encode("utf-8")
data = b"\x00\xfd\x05" + bytes([len(host_bytes)]) + host_bytes + struct.pack(">H", 25565) + b"\x01"
sock.send(bytes([len(data)]) + data)
sock.send(b"\x01\x00")
raw = sock.recv(16384)
response = raw[raw.index(b"{"):]
while True:
try:
result = json.loads(response)
break
except json.JSONDecodeError:
more = sock.recv(16384)
if not more:
break
response += more
sock.close()
print(json.dumps(result, indent=2))
This script returns JSON, but a more human-friendly result is this:
Server: Paper 1.21.4
Protocol: 769
Players: 40/120
MOTD: Sugar SMP
NEW SEASON WINTER
Secure Chat: True
That means the server uses Paper 1.21.4. MOTD stands for “message of the day”, the protocol 769 is the Minecraft Java Edition 1.21.4. The server also tells us there are 40 players online with a maximum of 120 players that the server can handle. Secure Chat refers to the enforcesSecureChat option, which requires all players to have a Mojang-signed public key to connect.
That means the suspicious player counts were indeed coming from the server. But that does not mean the number is accurate because the server itself could be faking it.
We continued with VirusTotal and OSINT of the sugarsmp(dot)com domain to find potentially related files or previously available downloads, so far with no avail (in case you are checking it right now: by now VirusTotal has more context information about related files for this domain because of our investigations).
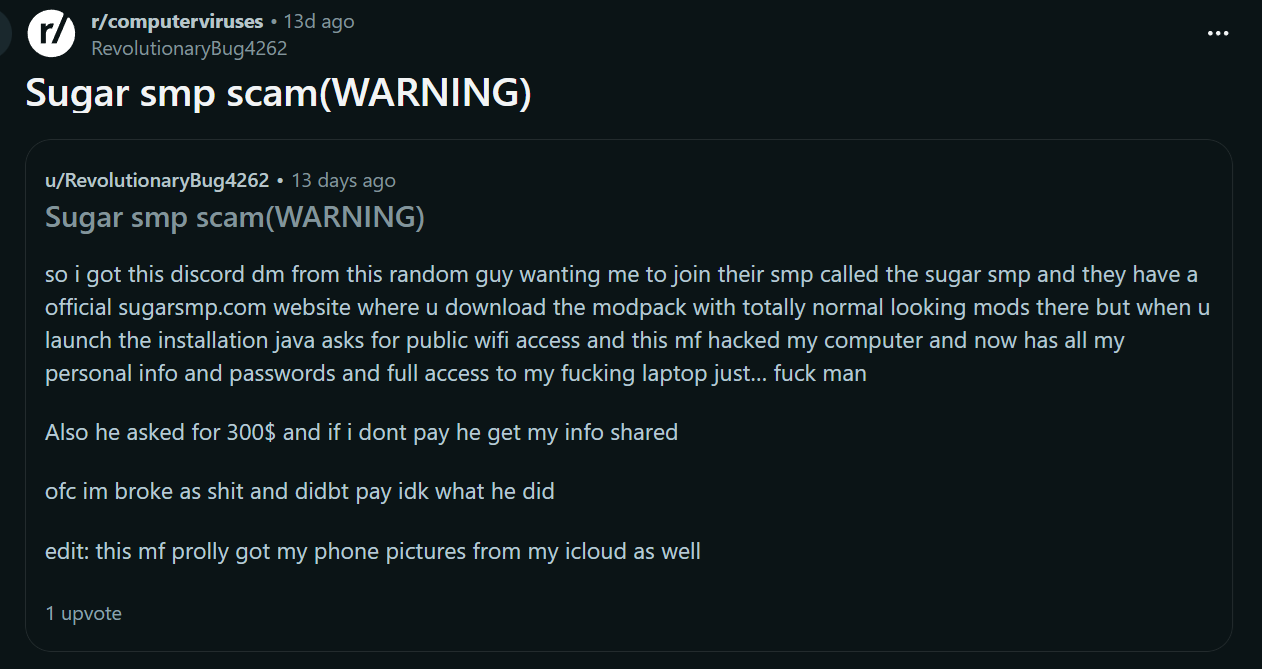
On 7th March the SugarSMP owner requested Reddit moderators of r/computerviruses to take down a post about infected files on their site. The scam warning post is from 27th February. In it, the user describes that not only their accounts and data were stolen after installing SugarSMP mods, but also that the SugarSMP owner extorted them for 300$ by threatening to publish private information.
We contacted the user u/RevolutionaryBug4262 and they replied that a "guy" had messaged them on Discord and invited them to their Minecraft server:
"[he] said the modpack download is there. I extracted the modpack zip into curseforge and looked over the modlist(was alr suspicious here) but it looks normal with just a bunch performance mods [...] when i launch the installation it has the whole ass ransom screen thing up but it got closed by alt f4 somehow but then he dmed me and said he has all my info and passwords bla bla bla(persumably malware logged the google saved passwords and pictures from icloud abd send it to him) and he still has control over my laptop until i disconnect wifi. oh yeah he asked for 300$ or else leak my info but he prolly gonna leak it anyways and im broke so i just changed my passwords and reset my computer"
According to u/RevolutionaryBug4262 this took place on February 26. They proceeded to send us two screenshots, which we will not disclose for privacy reasons. The first one shows a Discord message that was executed by a "scare" command. This message contains the text "YOUR COMPUTER WAS COMPROMISED". The second screenshot shows a typical stealer exfiltration message as threat actors usually receive them. It contained statistics about the amount of stolen cookies, passwords, credit cards and auto fill information and it listed the os, antivirus, HWID (hardware ID), IP address and showed as screenshot of the user's computer.
That means the owner of SugarSMP took down their own modpacks and replaced them with official modpacks between 26th February and 7th March, just in time for their appeal. This in turn means that a version of the site from before 26th February may tell us the truth.
Indeed, we had a breakthrough while looking at an early February 2026 Wayback snapshot of the SugarSMP website. We did not find links to the official Pokemon themed mods anymore, but links to SugarSMP-1.0.zip[1], SugarSMP-ModPack.zip[2] and SugarSMP 1.0.0.mrpack, which were hosted on sugarsmp(dot)com. At the time of writing, the first two files can still be downloaded via the Wayback archive. We continued our investigation with an in-depth analysis of the SugarSMP-1.0.zip modpack.
CurseForge modpackage analysis: SugarSMP-1.0.zip
CurseForge manages mods for you. Installers only need to list the mods by their project IDs in the JAR’s manifest.json, then CurseForge downloads and verifies these mods at install time, which means they do not take up space in the original ZIP file. Nevertheless the SugarSMP-1.0.zip[1] has a size of more than 20 MB, which seems too much for a bunch of project IDs.
In the manifest.json, the SugarSMP-1.0.zip lists indeed 15 legitimate mods by CurseForge’s project IDs. Among others Fabric API, Sodium, Iris Shaders and Simple Voice Chat.
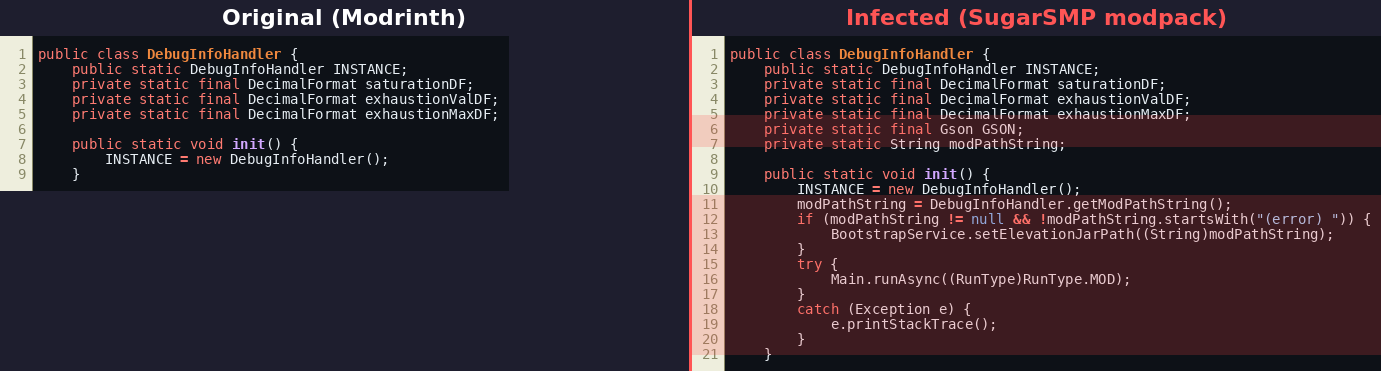
However, CurseForge’s modpack format copies contents from the overrides/ directory directly into the Minecraft instance without integrity verification. And in overrides/mods/ there is a file named appleskin-fabric-mc1.21.3-3.0.6.jar, which is AppleSkin mod by squeek502. This mod adds „various food-related HUD improvements”.
All legitimate AppleSkin classes under squeek/appleskin are indeed present and functional, but in squeek/appleskin/client/DebugInfoHandler.class the threat actor added a hook into the mod’s legitimate initialization flow.
When Minecraft starts, Fabric’s mod loader invokes the method AppleSkin.onInitializeClient() which in turn invokes DebugInfoHandler.init() with the injected malware code.
BootstrapService.setElevationJarPath() then records the JAR’s filesystem path, so that the persistence mechanism can copy itself later. Main.runAsync(RunType.MOD) launches the malware’s code on a daemon thread (a low-priority background thread) so that it does not block the legitimate code from executing.
RunType is a malicious class in org.spark. Since the package org.spark contains most of the malware code, we named this malware family Spark stealer.
Spark stealer uses an unknown obfuscator, which converts the encrypted strings into Braille Unicode characters and produces pointillist ASCII art such as the following.
I did not have the right font installed and therefore almost missed appreciating this ASCII art, which my code viewer translated into ‘\u2804’ style strings, but the amazement of my two collaborators convinced me to try a different font.
Below the Shrek art is a Discord webhook, which the malware uses alongside GoFile uploads to exfiltrate data. Spark stealer has variables for three different webhooks, one for primary data exfiltration such as credentials, token and generic system information, one for error reporting and one for crypto wallet theft. But this sample uses the same webhook for all three.
The Discord snowflake of the webhook dates it to 2026-02-04 00:34:43 UTC, which is only two hours before the sample was first seen on VirusTotal (2026-02-04 02:27:14 UTC).
The malware steals data from the following applications:
Discord tokens
Telegram desktop sessions
Wallet browser extensions
Local wallet applications
Chromium based and Gecko browser credentials
Steam credentials
Furthermore, Spark stealer queries social media APIs to fetch, among others, TikTok and Roblox session information, profile information, analytics or coin balances.
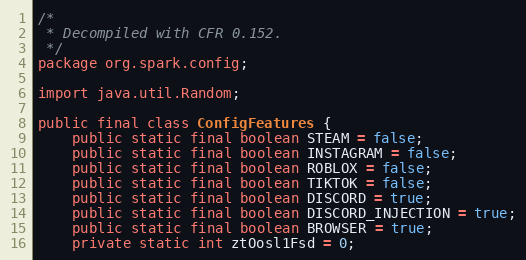
The main configuration of the sample is in ConfigFeatures.class, which in this case has most features disabled except for stealing browser data, Discord tokens and performing Discord injection.
Spark stealer has a keyword scanner, which looks for a list of words in stolen browser credentials, cookies and URLs. Notably these include sites like Pornhub and Onlyfans, which might be targeted to extort victims after infection. The keyword scanner also targets development and hosting platforms: github, replit, hostinger, cloudflare, ovhcloud.
One file in the root of appleskin-fabric-mc1.21.3-3.0.6.jar is named injection.b64 -- it contains encoded JavaScript code that the malware writes into discord_desktop_core/index.js. The Desktop client of Discord loads this JavaScript file, therefore executes the stealer’s injected code.
We deobfuscated the injected JavaScript with Babel Abstract Syntax Tree transforms. The code submits Discord payment sources, friends list, badges, server memberships and roles, and the creation date of the account to another Discord webhook. It monitors all outbound requests from Discord sessions and captures tokens, credentials and 2FA codes, login and password change events.
Both, the Discord injection code and the main stealer code, reference 25 custom emojis (see figure 7). They are part of the exfiltration message template that the stealer sends to the threat actor’s Discord server.

Because the stealer’s code relies on Windows APIs, for instance to decrypt Browser passwords (CryptUnprotectData, BCryptDecrypt, NSS_Init, PK11SDR_Decrypt), it uses Java Native Access (JNA) to call them directly from Java. This is an indicator that might be interesting for detection engineering, since Minecraft mods should not need any browser-specific crypto APIs like the ones in nss3.dll.
Persistence
There are three layers of persistence in total. Firstly, of course, every time the player opens the game with the infected AppleSkin mod, the malware launches.
Secondly, the code that is injected into the Discord client’s index.js survives restarts of Discord until Discord is re-installed.
The stealer’s method org.spark.service.system.BootstrapService.setStartup() obtains the path of the source JAR that was previously saved in the DebugInfoHandler. It creates the directory <user.home>\AppData\Local\Microsoft\Windows, and copies itself into that directory using the name FileExplorer.jar. Then it creates a scheduled task named “ExplorerStartup” which runs FileExplorer.jar.
Social engineering
The threat actor(s) go to great lengths to ensure the survival and reputation of their fake SugarSMP community.
When searching for “SugarSMP”, we find Minecraft server listing sites that praise SugarSMP as the best Minecraft server in 2026 and there is a supposed “Live Stream” on Youtube named “LIVE: Playing Sugar SMP Minecraft and GTA V”. The actual video content, however, does not make sense.
Only one search result is a cached scam warning of a Reddit user, whose accounts were hacked after installing the SugarSMP mods. After clicking on that search result, we only see a message that the post has been deleted by Reddit moderators.
Although we do not know the reason for the removal of this post, given that the moderators of r/computervirus were approached to take down warnings about SugarSMP (where it did not succeed), it is not unreasonable to assume that this social-engineering tactic may have succeeded in other subreddits.
The takedown request is believable because it came from a very long-standing, active and reputable Reddit user. After collecting more information about this Reddit user, we discovered that they have been developing popular mods for Steam games in the past years. Naturally we wondered if their Steam mod might have been infected too. We joined the mod community's Discord server and found an official announcement from other developers of the mod team that this user's account had been hacked. We contacted the new account of that user on Discord and they confirmed that their former Reddit, Google and Discord account got hacked and couldn't be recovered since. They too got scammed via Discord but not via the SugarSMP website. The stolen accounts are still in the hands of the SugarSMP threat actor(s).

A swarm of "sweet" Minecraft sites
One of my collaborators searched for “cute” and “cozy” terms and phrases that were used on the site and found plenty of similar sites with striking resemblance. The image below shows a gallery of our findings. The full domain list is in the IOC section.
While most of the sites are lookalikes, some of them feature a different, pink-ish or kitty-themed style.
We wrote a crawler that downloads the malware from all these domains. None of them were Spark stealer, but all of those with successful download hosted stealers at the time of crawling. We put a list of the downloaded samples at the end of this article.
The vast majority are Electron based stealers written in JavaScript. Two were also JAR applications but quite different from Spark stealer. Some are downloaders for Github parked stealers.
Clean download lure
In case of SugarSMP we were fortunate that the Wayback Machine preserved not only the website but also the malicious payload at the right point in time. We had similar cases with many fake sites in the past which impersonated official websites for tools such as DnSpy or PEStudio, but served clean files at the time of analysis.
It is also not the first time that threat actors have used social engineering to erase the fallout from their activities. They appeal to EDR / antivirus companies to get detections removed, they appeal to certificate authorities to reverse certificate revokations after spreading malware, sometimes they threaten with law suits and – in this case – they write to Reddit moderators to remove posts of their victims.
Threat actors do this because it works, which makes it even more important to be thorough while investigating such cases.
Remediation
Users whose systems might have been infected by Spark stealer should reinstall Discord, remove scheduled tasks that execute JAR files and scan their system with an up-to-date Antivirus scanner.
Furthermore, they should log out of browser and Discord sessions, regenerate the Discord backup codes for 2FA. Check Settings -> Authorized Apps and remove everything that does not belong there.
Any potentially affected passwords, like those stored in browsers, must be changed.
Transfer funds from potentially affected cryptocoin wallets to new wallets. Do not re-use any seed phrases for new wallets.
Spark Stealer hashes
[1] SugarSMP-1.0.zip - 060ed0ec27a0a4ad7b55425ed56d8ef0c55aa61b499d4884d1679f18d518ddf3
[2] SugarSMP-ModPack.zip - dfef4a07800ad08e09390291647e4cf50c77d1a83e076c181103f25a77dd5697
[3] Similar Spark stealer files
7ec97405aeb271c73a7bbb9d466f755c18921f16403dab581e79d1096aadfd03
495d1d500afc5ec700a0a15bf34862973e8e0152f9346b322a468cbe6e7c9d1e
06e12e4393c9554c81bd087446e32890a45fc77ab6f048e0dd0db1d4cc010f1f
7115dcd7a17c6d5f4e01d72a7056a6f7e9a9ea7556b6f8fce02be0b97f632ddf
424a1ab33890d6c6448dfc25507ac17d48e7d406caf287c62082225ef1c5358d
1a6bceaf9e4efe70144984dc76be7c9d0ffcfaaeb76325a4394f6eb14e3a5135
67e3dbde303c8fc70020ee94c0036a1499f34d029655f6f1d156fbe002125470
7365bb5c74edcbf71977b31280d69aed7e6a49c8a80ab8076fef84f138df98e4
deef632b35470738485067d3c757d1fdb7e45393b59010ce170e69c23b3a092d
b59ded7da641637ec3a95fe78b8b1c69d7a85bb9a70351e80f26b334fe452699
90b6a76843e74362c92ef691a0d078a5cc0cdc2a396ecf1b63eae7291215faff
74064d191ab454bbf75e899e4097332d4a8897b13c448db02022c662135e8405
d6832ecc0d04a0621fbe1ed19311577f6a750bfb68460809bc9dfa571c222206
85892a04d28e1962511c2aa4ffd5e9ef3e34e4280a2022427d617d884fa1e774
e4598c17b948526ccc3f586857363a75c95e695a5125d5b4fed088b27a58100e
16ca5165e297c6c20003186943571394173249f10e376f4d1c085304f5cca087
8c2c4ff54b48631d324b643a333ae08161a091f439cfcb684cdf2157a42c9912
5b573de08c6980957556c94666e81544cdb0d084e9e880cb32c937a851274930
0221d06009b9848a3e1be34405fef1d586b84d115f10109de8f9c2e4806b6f40
85872d267e1125e8bba0c460a8a7416d0845e9794a49a90a0dde8c9401f07a03
2a4ee7edcd12ea727af4eec78ae4e15620678cb9a53b53630acb7144097efb11
"Cozy" Minecraft domains
bunnycraft(dot)online
cherriecraft(dot)com
cutiecraft(dot)network
cutiemc(dot)com
cutiesmc(dot)com
cuttiescraft(dot)com
cuttiesmp(dot)com
greatsmp(dot)com
hellocraft(dot)online
hellokittycraft(dot)net
hellokittymc(dot)online
hellopink(dot)net
kitllycraft(dot)net
kitlycraft(dot)net
kitseramc(dot)com
kitten-smp(dot)com
kittenclient(dot)com
kittenmc(dot)com
kittensmc(dot)com
kittiemc(dot)com
kittieslandmc(dot)com
kittiysmc(dot)com
kittlycraft(dot)com
kittlycraft(dot)net
kittycraft(dot)com
kittycraft(dot)online
kittycraft(dot)site
kittypinkiecraft(dot)com
kittypixel(dot)com
kittyscrafts(dot)com
kittysmp(dot)net
kuromicraft(dot)online
lanchemc(dot)com
minicraft(dot)world
mysticraftsmp(dot)fun
neekocraft(dot)com
owocraft(dot)com
pinkcraftmc(dot)com
pinkiecraft(dot)com
playpinkycraft(dot)com
playsweetcraft(dot)site
ponyrise(dot)com
ragnacook(dot)site
sanriocraft(dot)online
sanriomc(dot)com
sanriomc(dot)online
softiecraft(dot)com
sugarsmp(dot)com
sweetcraft(dot)net
sweetiecraft(dot)net
uwucraft(dot)net
"Cozy" Minecraft stealers
19645fc596fd49196581f751f9217030d5bec9eb10d1d836668407e0304730aa
225f57aba3250d648e7bc4ad51b533552a3a0e0425817d02b1d3b668fddf78bc
28a03d29e99c75fc9603b9e5193f97feca561bdc6db4271cdb2d522b9d5b2ae3
2c5fb4e1b75c2a26e9e186069d61e8204c7dc8752d3b9b95087b19b1020df691
38c55481911e7f789fc68628c7b9d9a2f8139524ac2deffe85ffe3ac9dce8178
4c52f12b45f5c0afb3684647222419332c1627ea95af03553fdd9e3a509d272b
52601d295b5468aa9e2db1802fe55dab437128584df4f20e9bac164ac4ec8ec3
53e059cab287674515454b51f4dda281d0812a51fff2c9c7f9b077d3a475600a
54f00324f7070a9a7308fdea9eaaa58e96e96273608a75db5bacdd410f50f0c0
5620216dc128a3d9292defee29b7f295c33eda97e5be9a0eede777d9d70efae5
62528f64a6515df67129ca7bea4cca43b01146d2d166cc3b0bd890f27efc38ea
6961710721e74d9b3f28dd595b01abc7ee71f0d8339b4cf95679435601302ae6
69cfd3024bb89fc2f7fdeb87c77b35bf8216e31c2146161f0b3dfaec25da771f
6e843f82431acbcb35dffcb1a5ae40ef4c1127e9ae6f2e5f738e7355d3a89ceb
7b9b75d7febf015003ac167e122b0cdfc561883b725252d593a85a42eba4b6bc
7e7c533bd42d386d95e6bd299efc1ad3ef5ea58e69c08bdd2d02fc97e89e0e53
7f239306e6e32246a07818b3600932c1ad85a42e9902370d98d9fc0f1b120ec7
8e79a1a6e6df1f622fbbd2bde9fe19f93340da2bd1be6d70b91fd62dce5e74e0
997f7449d7b98aa08ad37c7953a51ad3f95e7532824959b7eba3953b30e76475
a3e88f95484965f7c9a34731ffca42fcaea25e917f5a6d70ab86c941cf23b832
c08c9be47baddbb62f69b70932221d89f8a9984c778b762212676c470ba329cb
c4fc36d968c0c190716ecefac4f8fdea92de88fd94080108ef85a96512eb6471
ca48b83c93875285dd66ba33e11a5483b193d605da924b126e96cf4034c28e67
d9ad0330531ddf455438714192de9b3c7755d50acf939cb4de97ba6fb39fb1ae
e340d345dfd492393971c8602fd4863583247fa46cd834fe5e87258d18fc2eac
f45a28e7a6d64bfb4e74d6ffed115e79afb005d5c33dfcd1045b068c03b0e480
f8002a0a621bf26d562c8cca86acb490084648379a8f9340f3329eeaa9124685
fa2a590dfdbc9170be58764f8da6a27a81d551b00a21061a9dc03bfab78f9e63