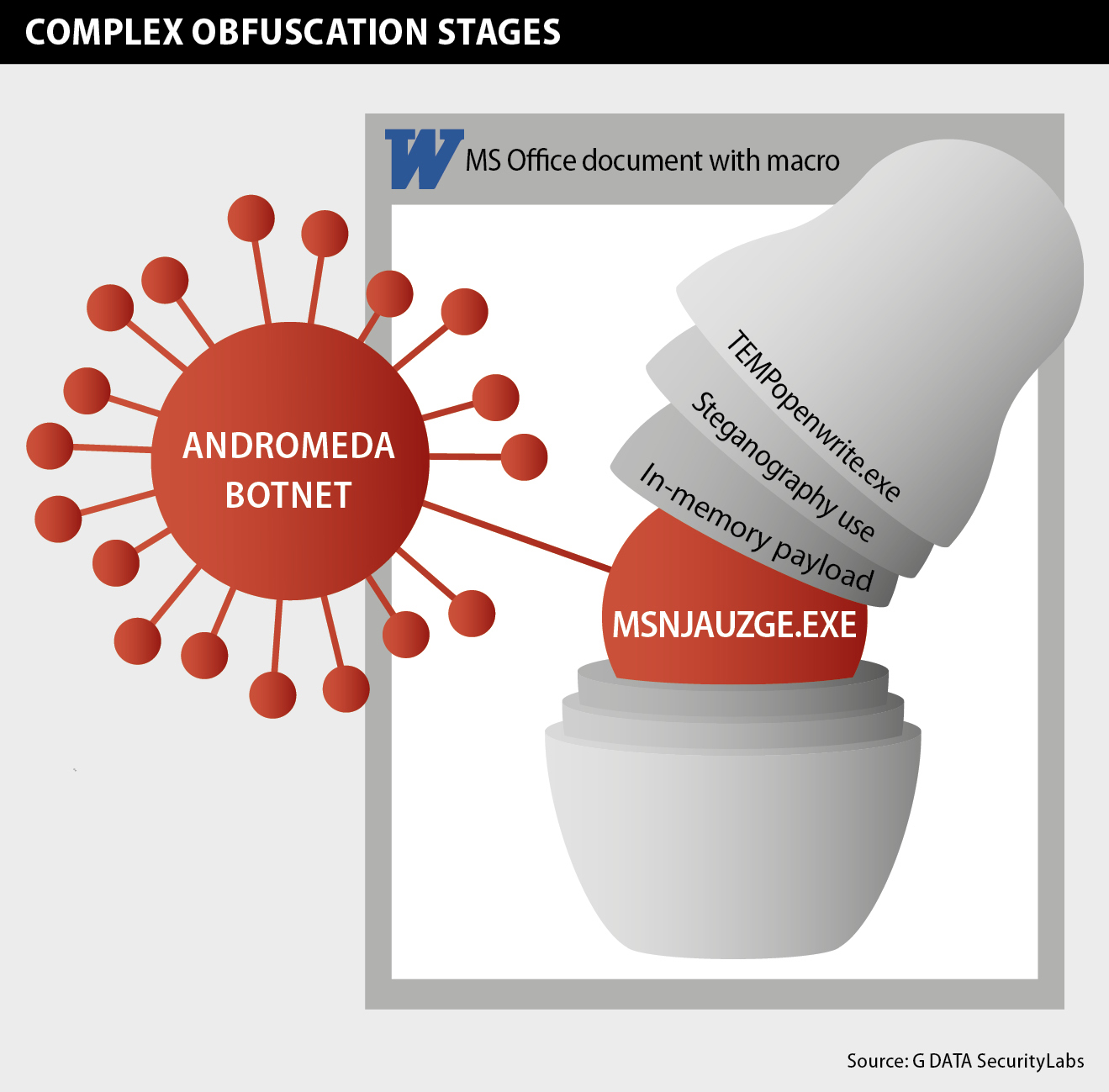
Case 1: The complex sample with Matryoshka-like behavior
First stage: Macro in MS Word document
The beginning of the attack is carried out via a crafted MS Word document. In many cases, such a document is spread via spam emails. In this case, the document’s name suggests that the file poses as a contract, its name is umova-3828.doc and “umowa” means contract in Polish. As soon as the document is opened, the following message appears in case the user does not allow the automatic execution of macros:
As we can see, an official security warning appears. This warning explains that the execution of macros is currently disabled and provides a button to enable the use of macros in the document.
The written content of the document also suggests enabling macros. Interestingly enough, the attackers use an incorrect plural form of macro and some users might be alerted at this point.
In any case: We recommend you do NOT enable macros in such a situation, handling a foreign document from an unknown source, no matter what the text suggests.
The screenshot below shows parts of the macro’s source code, embedded in the document:
The purpose of the first stanza in this code is to generate a file name. In our case, the file name is TEMPopenwrite.exe (see line 35). A noteworthy instance: We presume the malware author made a mistake and forgot to insert a “\” in line 35 which results in the name of the file being TEMPopenwrite.exe instead of openwrite.exe in the directory TEMP.
The purpose of the rest of the code shown is to extract data from the Word document, decode it and store it in the file previously generated. Finally, the last line allows executing the binary previously extracted.
Second stage: Steganography
Steganography is the practice of concealing a file or message within another file.1
TEMPopenwrite.exe is an interesting packer, coded in .NET. The main purpose of TEMPopenwrite.exe is to extract a stored resource, a bitmap image stored in its .resource file. From each and every pixel of the bitmap image, the R, G and B values are used to build up a byte array which is then deobfuscated/decrypted:
The result is a new .NET file, which we will now call Binary2, which is then loaded and executed.
Third stage: planting the payload
Now, we are looking at the third stage, involving Binary2. After its execution, it stores a payload directly into the memory, using the function VirtualAlloc(), and jumps to it in order to execute it. The snippet below shows the payload and the use of VirtualAlloc():
Fourth stage: the payload in action
The payload is considered as the fourth stage of the dropper. Its first task is parsing the original .NET binary, TEMPopenwrite.exe. It reads the .exe code, checks a specific location within the code and then decrypts data from that location. The snippet below shows the part of the payload that is used to read TEMPopenwrite.exe:
The extracted data is decrypted and stored on the machine in directory %appdata%, named msnjauzge.exe.
Fifth stage: the actual infection of the system
As a last step in this infection chain, msnjauzge.exe is executed. With its first execution comes an autostart entry in the registry to make it survive system reboots.
This file is, so to say, the innermost of our Matryoshka dolls.
Case 2: A much simpler approach
We got to know about Word documents posing as invoices for the German discount subscription program offered by Deutsche Bahn, the German national railway company. Those documents were sent as attachments of spam emails and come with a name like BAHNCARD_5268.doc or similar.
The sample we analyzed shows a behavior very similar to the complex sample of case 1 – at least when it comes to the beginning and the end. The macro embedded in the MS Word document is exactly the same, with one exception: it does not drop a .NET file but a PE32 executable. The macro then executes this dropped PE32 file and this directly finds and decrypts the data stored within the PE32 to generate msnjauzge.exe, as seen before. In the end, the exact same file msnjauzge.exe is delivered to the machine, to enlist the PC as new zombie PC in the Andromeda/Gamarue botnet.
msnjauzge.exe: the resurgence of a well-known botnet
The file msnjauzge.exe is the entry point to a well-known botnet called Andromeda, also known as Gamarue. This botnet is known to have delivered the ZeuS banking Trojan in 2011.
In our case, the C&C contacted by our sample is hxxp://ss77.37to.ru/mail/inbox. By the time of writing this article the server has been waiting for connections. It did not yet deliver additional code to the infected analysis machine. Therefore, the intended use of the botnet cannot be determined yet.
Conclusion
We assume that the creator of this botnet is “collecting” many infected machines to sell the access to them on the black market. The buyer will be able to drop whatever he wants to drop on the compromised machines of this botnet (e.g. banking Trojans, spyware, spam bots, …).
We saw that everything started with simple documents – file types which are usually assumed as safe and not dangerous at all, used on a daily base on private and corporate machines worldwide.
We strongly recommend you check the configuration of the macro settings on your machine (see below) and that you NEVER let macros execute automatically but decide it manually. Moreover, we recommend to never allow macro execution within unknown documents at all.
In the complex sample we saw, the malware author uses many obfuscation techniques and stages in order to hide the resurgence of the old Andromeda/Gamarue botnet in 2015. The image of the Matryoshka dolls perfectly fits the author’s approach. The other approach carried out the infection rather straightforward.
This botnet seems to be at the beginning of its lifetime and does most probably not yet count millions of infected systems, which we derive from the rather low level of different samples identified for this campaign during the analysis phase for this article. But it is difficult to predict the evolution of this botnet.
---
What is a macro?
Microsoft Office documents (for example Word, Excel or PowerPoint) can embed code. The language used to code macros is Visual Basic for Application (VBA). The purpose of a macro is to improve the document handling, for example the creator of the document could create a macro in order to automatize repetitive actions. Unfortunately, macros can not only be used for positive actions, but can be also used by attackers in order to execute code on a targeted system.
Microsoft added security mechanism to avoid malicious use of macros: In case a document contains a macro, the macro is not executed automatically and the user is alerted by a notification as shown in the screenshot above, shown in case 1. The user must accept to enable macros to execute the code embedded in the document.
Checking your current macro settings:
To check your current default configuration in MS Word, you can click on File, and Options and choose the Trust Center menu and click Trust Center Settings, and then click Macro Settings. We recommend that you choose “disable all macros”, allowing the system to alert you by choosing the option “with notifications”.
Samples analyzed
| Case 1 | |
|---|---|
| Word-Document | SHA256: A019BB125EC3F9F5FE2944681F16BF798264F70135DD7361361E19F934F93700 Detection Engine A: W97M.Dropper.C Detection Engine B: Macro.Trojan-Dropper.Sesorm.A |
| TEMPopenwrite.exe | SHA256: ACEFC3DD92B911B80F4C09A3CE89635D3F55BB2A7D881C42055ED8F67EBE19B7 Detection Engine A: Trojan.GenericKD.2168928 Detection Engine B: Win32.Trojan.Netryoshka.G |
| Binary2 | SHA256: 12D25E7A578188AE654527B6DF89AAA8D755EA26D15430E6421BF23CB9A9CA43 Detection Engine A: - Detection Engine B: Win32.Trojan.Netryoshka.E |
| msnjauzge.exe | SHA256: 3913D5568D616A4810DABADE844D9BAE2BFE4F6F588BC70B1F4C33F3D617389A Detection Engine A: Gen:Variant.Zusy.129227 Detection Engine B: Win32.Backdoor.Netryoshka.A |
| Case 2 | |
|---|---|
| Word-Document | SHA256: 85342505474C2E7A62B958EFB417CF638694E89A9016AFD23224032F84E861E6 Detection Engine A: Trojan.VBS.Agent.JH Detection Engine B: Macro.Trojan-Dropper.Sesorm.A |
| Dropped PE32 | SHA256: 1023296F88F88BBB77D579F5FBAD02E064274264C506639D7829ADA1B55C89F6 Detection Engine A: Worm.Gamarue.B Detection Engine B: - |
| msnjauzge.exe | SHA256: 3913D5568D616A4810DABADE844D9BAE2BFE4F6F588BC70B1F4C33F3D617389A Detection Engine A: Gen:Variant.Zusy.129227 Detection Engine B: Win32.Backdoor.Netryoshka.A |
Links zum Artikel:
[1] http://de.wikipedia.org/wiki/Steganographiede.wikipedia.org/wiki/Steganographie
G DATA Matrjoschka-Grafik als RGB, 430KB
G DATA Matrjoschka-Grafik als CYMK, 1170KB